Days after going public with the flaw that became known as PrintNightmare, Microsoft is back with another complicated alert: the flaw can affect all versions of Windows. The information appears in an official report from the company’s security research center, which also indicates mitigations and protective measures against a vulnerability that is still being investigated and remains unpatched, while being actively used by criminals.
Initially, it was believed that only server versions of the operating system were vulnerable to CVE-2021-34527, which allows remote code execution, with administrator privileges, from the Windows remote printing system. However, all recent operating system versions have the programming components that allow this attack. Days after the breach was revealed, confirmation came that any edition can be attacked in this way.
More specifically, the vulnerability was detected from Windows 7 Service Pack 1, also through Windows 8.1 and different editions of Windows 10. As already mentioned, versions of the operating system for servers start from Windows Server 2008. Machines of 32 and 64-bit can suffer the attacks, as well as packages for ARM processors.
The problem appears in a resource called Print Spooler, which manages queues of documents sent remotely for printing. From the breach, a criminal can create new accounts with administrator privileges, collect files from victims or send malware to the network and devices, with new attack vectors opened from these routes.
Two factors make the breach more serious. First, according to Microsoft’s report, this is a low-complexity exploit; second, a proof-of-concept detailing the attack was published ahead of time. Security researchers from the specialized company Sangfor pointed out a communication failure with Microsoft and disclosed the breach’s details on GitHub. The code was quickly erased, but it was forked before that and, for experts, should be considered public.
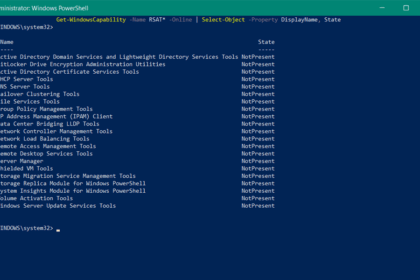
This proves that, even before updating the information about CVE-2021-34527, Microsoft was already warning about attacks involving the vulnerability. While an update is not released, the company released indicators of compromise and recommends that users, mainly corporate users, disable the Print Spooler service or, at least, the remote sending of documents to the print queue – needless to say, in many corporations, this is a big problem.
There is no forecast for releasing an update for the PrintNightmare flaw. In addition, with the confirmation that all recent versions of Windows are vulnerable, the question remains about the operating system versions that are no longer supported, as is the case of Windows 7, whose life cycle ended in January last year.
Source: Microsoft