User accounts are frequently created for various purposes, such as granting access to specific resources for external companies or visiting auditors during installations. However, these accounts are not uncommon to be forgotten and left active even after they are no longer needed. This poses a security risk that should be addressed.
To mitigate this risk, limiting the activation of such accounts from the beginning is recommended. One way to achieve this is by temporarily activating users using Powershell. By doing so, you can ensure that these accounts are only active for the necessary duration, reducing the likelihood of them being forgotten and posing a potential security threat.
Activate user account via Powershell for a limited time
You can set a time limit for user accounts through the graphical interface, specifically the “Active Directory Users and Computers” tool, or by utilizing PowerShell. This functionality allows you to specify an expiration time for an account.
It’s important to note that setting an expiration time does not deactivate the Active Directory (AD) account entirely. Instead, it denies login access to the account once the specified period has elapsed. This approach provides a means to restrict user access while keeping the AD account active for administrative purposes or other relevant tasks.
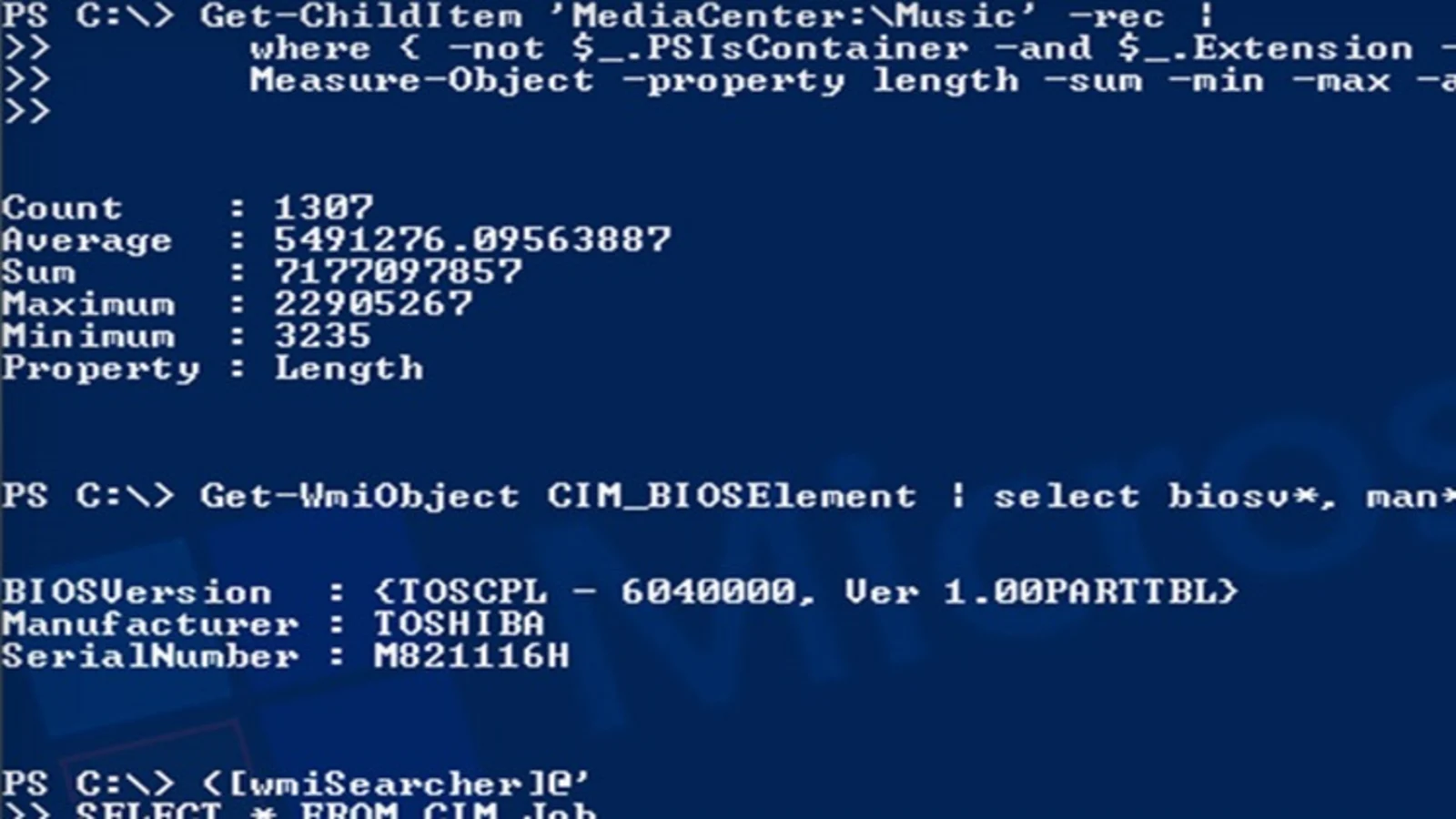
In the following example, I first activate a user account and then configure it to allow login for the next 7 days.
enable-ADAccount -Identity <UserName>
get-aduser -identity <UserName> | Set-ADAccountExpiration -TimeSpan 7.0:0 The time span is entered in the format .::. A look at the AD user administration is enough to check:
As an alternative to the TimeSpan parameter, an exact expiry date can also be defined. The command for this would be, for example:
get-aduser -identity <UserName> | Set-ADAccountExpiration -DateTime 31.12.2018Why temporarily activate a user via PowerShell?
This approach is especially beneficial in situations where users require intermittent access to the system. With the convenience of a PowerShell script, you can swiftly handle this task. Simply save the script and execute it whenever necessary, and the access will be promptly deactivated.
This method proves particularly valuable when dealing with interns or external employees whose roles frequently change. It effectively prevents the accumulation of orphaned user accounts, which can be a common issue in some IT environments.
By implementing this approach, you can ensure inactive accounts are swiftly deactivated, avoiding any unnecessary clutter and potential security risks associated with lingering “dead files.”