Windows 11, the latest operating system from Microsoft, is set to be officially released on October 5, 2021. However, there is still some uncertainty surrounding the minimum requirements to run the system smoothly. One of the key components on the list is TPM 2.0, a feature that has generated confusion among consumers due to its limited information and discussion from the company.
TPM 2.0, or Trusted Platform Module 2.0, is a security feature that provides hardware-based protection for sensitive data and system integrity. It safeguards against various attacks, such as unauthorized access and tampering. While the inclusion of TPM 2.0 in the Windows 11 requirements aims to enhance overall system security, its introduction has raised questions and concerns among users who may not be familiar with this technology.
What is TPM?
The Trusted Platform Module (TPM) is an essential component in computer systems that enhances security measures during the startup process and ensures the integrity of the operating system. It is an integrated cryptographic processor on motherboards that provides advanced security features.
During system startup, the TPM plays a crucial role by receiving and securely storing encrypted hashes and data mapping algorithms generated in the startup process. These hashes are isolated and protected from other components in the system. Only the TPM chip itself can decrypt this information.
The TPM generates a unique Storage Root Key (SRK) at each startup, strengthening the system’s security. This key is crucial in protecting the PC’s information, even in the event of a processor or firmware hack. It acts as a safeguard, ensuring that the contents of the TPM cannot be accessed by any other component or software, including the Windows 11 operating system.
In Windows 10, the TPM is utilized for automatic startup processes, offering an additional layer of security. Microsoft advises against manually configuring the TPM through code, except in specific cases such as system resets or clean installations. This precaution ensures that the TPM functions optimally and maintains the desired level of security.
By leveraging the capabilities of the TPM, computer systems can benefit from enhanced protection against unauthorized access and tampering. The TPM contributes to a more secure computing environment, safeguarding sensitive information and maintaining the system’s integrity.
Do I have TPM 2.0 on my computer?
The Trusted Platform Module (TPM) initially made its way to laptops in 2006, but it took some time to become available on desktop computers. Nowadays, newer motherboards come with an integrated TPM chip. However, it’s important to note that in many cases, the TPM is disabled by default and needs to be manually enabled in the BIOS settings.
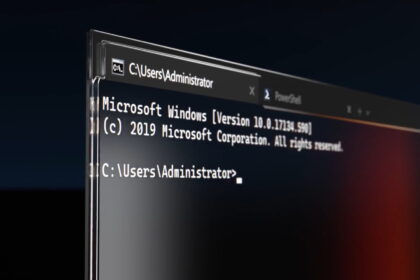
If you’re unsure whether your machine has the TPM 2.0 chip or if it’s enabled, you can follow these steps to check:
1. Press the Windows + R keys to open the Run dialog box.
2. Type “tpm.msc” in the text box and press Enter.
3. This will open TPM Management on your local computer. If the TPM is detected, your system is compatible with Windows 11. If not, you will see a screen indicating the absence of the TPM.
You can also check the TPM feature in the Windows 10 settings menu. Here’s how:
1. Open the System Settings search bar or click the Start button.
2. Type “tpm” in the search bar.
3. Select the “Security Processor” option.
4. If the sheet appears blank, your motherboard’s TPM is not enabled.
If you have TPM and its not Activated, you can follow this guide to activate TPM 2.0.
In August, Microsoft itself recommended following these two methods to verify the presence and activation of the TPM module. You can refer to the official article for more information. However, please note that the activation process may vary depending on the motherboard manufacturer’s instructions, which are typically provided in English.
TPM can be enabled in BIOS
If your PC doesn’t have the Trusted Platform Module (TPM), there’s still hope, even if the component is not present. You can explore your system’s BIOS settings to search for TPM options as a last resort. Accessing the BIOS menu may vary depending on your motherboard/CPU, so paying attention to the specific instructions is essential.
For Intel processors, the encryption technology is known as Intel Platform Trust Technology (PTT), which functions similarly to a dedicated TPM chip. On AMD Ryzen CPUs, protection is provided through fTPM (TPM firmware), which is software-based and integrated into the component.
It’s worth noting that these features are often “hidden” within the BIOS menus. To locate them, it is recommended to check your motherboard model, find the relevant part manual (preferably in PDF format), and use the Ctrl + F shortcut to search for the acronym TPM. This should help you identify the exact location to enable the feature. Once you’ve made the necessary changes, save them and restart your machine. After the operating system loads, you can repeat the verification process mentioned earlier to ensure the TPM is now detected.
If none of these solutions work, you have two remaining alternatives. Firstly, you can purchase a separate TPM module online, manufactured by companies like Asus. Alternatively, you can upgrade to a modern motherboard with the TPM chip.
While the TPM requirement aims to standardize security among Windows users, it may leave older computers out of the compatibility list.
However, it’s important to note that Windows 10 will continue to be officially supported until October 14, 2025, providing an extended timeframe for users to stay on the supported operating system.