Microsoft is preparing a significant security overhaul in its upcoming April 2026 update for Windows, introducing stricter controls for network authentication that could impact enterprise environments if not properly configured.
The change centers on Kerberos, the authentication protocol widely used in corporate networks, particularly in Active Directory environments.
Shift to Stronger Encryption Standards
Under the new update, Windows will enforce the use of AES-SHA1 encryption for Kerberos authentication in cases where encryption types are not explicitly defined. Previously, such scenarios defaulted to older and less secure methods like RC4.
This transition is part of Microsoft’s broader effort to eliminate legacy security protocols and reduce exposure to vulnerabilities associated with outdated encryption standards.
Impact on Enterprise Systems
The update may affect organizations using FSLogix, a profile management solution that stores user data in virtual disk containers on network shares.
Systems that rely on:
- SMB file shares linked with Active Directory
- Kerberos authentication configured with RC4 or undefined encryption
- Legacy infrastructure lacking AES-SHA1 support
could face authentication failures after the update is applied.
Microsoft clarified that the issue stems from platform-level changes in Windows itself and is not directly tied to services like Azure Virtual Desktop.
Timeline for Enforcement
The rollout will follow a phased approach:
- April 2026: Enforcement mode enabled by default on domain controllers. Systems will begin using AES-SHA1 exclusively for accounts without defined encryption settings. A temporary audit mode will remain available for rollback.
- July 2026: Audit mode will be removed, making enforcement mandatory with no fallback option.
This timeline gives organizations a limited window to audit and update their environments before stricter enforcement becomes permanent.
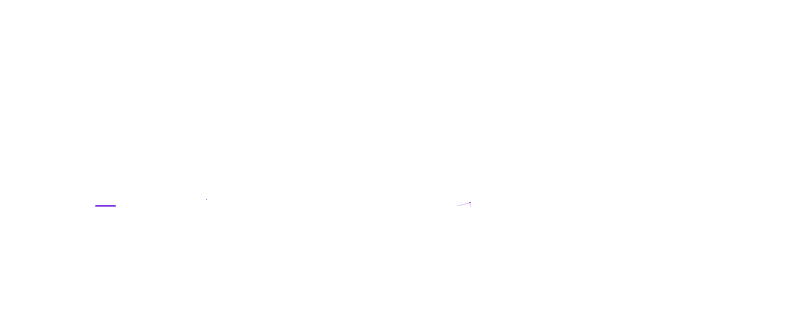
Guidance for IT Administrators
Microsoft is urging IT teams to proactively identify systems still using RC4 or undefined encryption settings within Active Directory, particularly those tied to SMB-based profile storage.
Recommended actions include:
- Updating encryption configurations to support AES-SHA1
- Testing authentication workflows in advance of enforcement
- Ensuring compatibility across domain controllers and connected systems
Failure to make these adjustments could result in login disruptions and access issues for affected users.
Part of Broader Security Push
The Kerberos update is one of several recent steps by Microsoft to strengthen Windows security. The company has been actively:
- Addressing vulnerabilities in domain controller authentication
- Phasing out NTLM in favor of more secure alternatives
- Tightening controls around legacy drivers and system components
These changes reflect a continued push toward modern security standards as organizations face increasingly complex cyber threats.
While most everyday users are unlikely to be affected, enterprise environments with older configurations may encounter disruptions if updates are not applied in time.